7SHIELD 1st Newsletter
Introduction
Dear Reader,
We are delighted to present you the first newsletter of the Horizon 2020 project 7SHIELD – “Safety and Security Standards of Space Systems, ground Segments and Satellite data assets, via prevention, detection, response and mitigation of physical and cyber threats“.
7SHIELD aims to develop a flexible and holistic security framework covering all macro-stages of crisis management (prevention, detection, response, and mitigation) to protect European Space Ground Segment infrastructures against physical, cyber and hybrid threats.
This project started on the 1st of September 2020 for a 2-year duration.
7SHIELD is led by a consortium of 22 partners from 12 different countries, composed as following:
- 5 operators of Space ground segment systems

FMI
Finland

SpaceApps
Belgium

DEIMOS Space
Spain

SERCO
Italy

NOA
Greece
- 3 first responders and policy organizations

KEMEA
Greece

Hellenic Police
Greece

EETT
Greece
- 3 academics & research institutions

CENTRIC
United Kingdom

CERTH
Greece

CeRICT
Italy
- 11 industrials & technical companies

CS GROUP
France

ENGINEERING
Italy

ACCELIGENCE
Cyprus

Cyberlens
Netherland

DFSL
Israel

INOV
Portugal

Resilience Guard
Switzerland

RESILTECH
Italy

SATWAYS
Greece

CS Novidy’s
France

DEIMOS Engineering and Systems
Spain
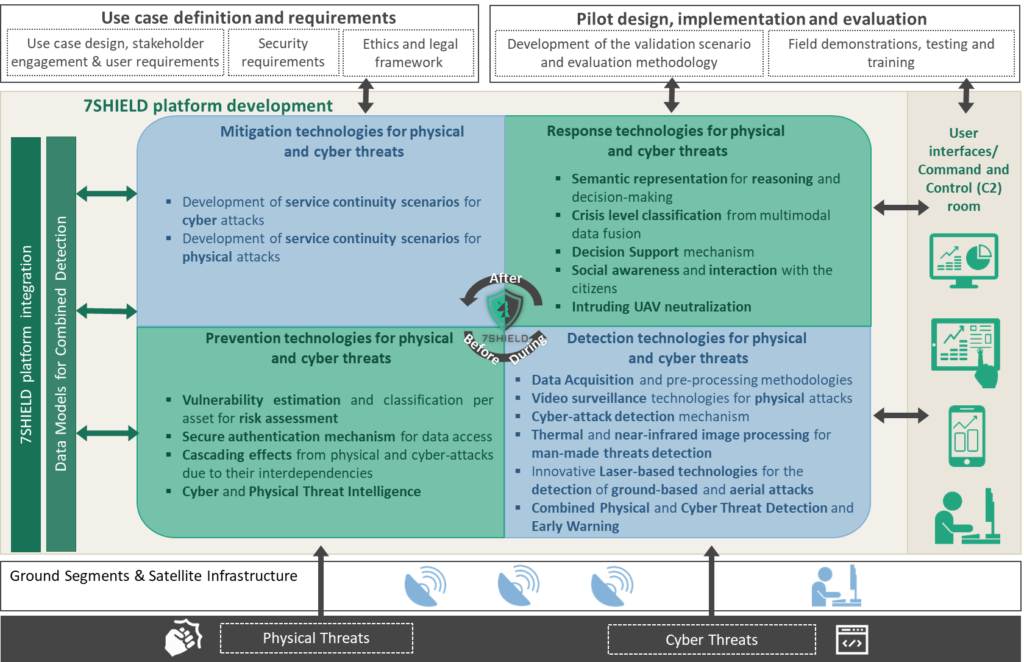
7SHIELD Concept
The overall concept of 7SHIELD is illustrated in the figure below. The expected result will be an integrated yet flexible and adaptable framework enabling the deployment of innovative services for cyber-physical protection of ground segments.
Major achievements
Several major achievements have been made by 7SHIELD partners during the first year of the project. The main ones are listed below.
Achievement #1 – 7SHIELD integration to the European Cluster for Securing Critical Infrastructure (ECSCI)

The 7SHIELD consortium has become a member of the European Cluster for Securing Critical infrastructures (ECSCI). ECSCI is a cluster of H2020 research projects dealing with security of Critical Infrastructures. Its main objective is to bring about synergetic, emerging disruptive solutions to security issues via cross-projects collaboration and innovation. The cluster will research how to protect Critical Infrastructures, highlighting differences (approaches, sectors of interest, etc.) between the clustered projects and establishing tight and productive connections with closely related and complementary H2020 projects.
7SHIELD consortium is involved in the common debate on the protection of Critical Infrastructures with the other projects, identify potential synergies and participate in joint workshops and events.
Achievement #2: Design of the 7SHIELD Pilot Use Cases
The end-users of 7SHIELD – namely the Finnish Meteorological Institute’s Arctic Space Centre, Deimos Space, the National Observatory of Athens, Space Applications Services, and Serco Italia – have successfully designed five Pilot Use Cases for the demonstration of the 7SHIELD prevention, detection, response and mitigation technologies at their Ground Segments in Finland, Spain, Greece, Belgium, and Italy respectively.
The Pilot Use Cases, which have been designed with the support of 7SHIELD first responders and technical partners, include the simulation of various hypothetical scenarios of cyber, physical and combined attacks. Such scenarios include the intrusion of a potentially hostile Unmanned Aerial Vehicle into the premises of the Arctic Space Centre in Sodankylä in Finland, malicious access to the facilities of Deimos in Spain and cyber-attack attempt at its data centre, unauthorized access to the data centre of the National Observatory of Athens and installation of a jamming antenna in Penteli, as well as simulated Distributed Denial of Service (DDoS) attacks at the ICE Cubes infrastructure of Space Applications Services and at the ONDA DIAS platform operated by Serco.





Achievement #3: Definition of the user, security, and ethical requirements
Another important achievement of the first project year is the definition of the user, security, and ethical requirements that have guided the design of the 7SHIELD architecture and the development of its different physical and cyber-security technologies. The requirements cover a broad spectrum of specifications, from end-user needs (in terms of functionalities and performance of the 7SHIELD modules) to security and ethical aspects in line with existing national and European regulations, and international standards. The requirements were defined through a dedicated elicitation process that included multiple interviews, brainstorming sessions and focus groups with the participation of direct users from the Ground Segments, as well as stakeholders and First Responders specialized in Critical Infrastructure security. Last but not least, a preliminary ethics and legal framework has been defined, to inform the partners and ensure the ongoing compliance of the project and the developed system with ethical, societal and legal standards.
Achievement #4: Design of the 7SHIELD System Architecture
The design of the 7SHIELD System Architecture is based on the User Requirements and Use Cases Design defined in the context of WP2. Moreover, the system requirements have been used as input for the design of the 7SHIELD System Architecture. The identified system requirements have satisfied the user requirements providing a clear understanding of how the 7SHIELD architectural modules will transform user needs to delivered features.
The 7SHIELD architecture design approach is based on the main architectural views:
- Logic Architectural View (LAV) that identifies all the functional modules and components which are part of the overall system. The main interactions between the architectural modules have been also defined along with the main entities from which data are collected (7SHIELD Data Sources) and to whom services are provided (7SHIELD Users) through innovative Graphical User Interface (7SHIELD Devices).
- Integration Architectural View (IAV) highlights all the interactions among the concrete components according to the user requirements), the system requirements and the logical architecture, focusing on the integrated prototype of the 7SHIELD system as a whole. To better define IAV, each module will be further detailed through an interoperability form to better explain which modules interact with each other.
- Deployment Architectural View (DAV) provides a guideline on how to deploy the integrated system and its components.
The 7SHIELD architectural design has been defined with the aim to be as much modular and scalable as possible to integrate on one hand all the leading-edge solutions developed throughout the project and on the other hand existing SGS-specific protection solutions already in place.
The architectural style chosen to represent the 7SHIELD Logic Architecture is the layered style. It offers outstanding benefits in terms of modularity, interoperability, functional decoupling, flexibility, and reuse. Moreover, the layers allow for a clear isolation of concepts and functionalities that are loosely coupled, which in turn ensures flexibility, scalability, and maintainability of the entire 7SHIELD system architecture.
Architecture will identify the components responsible for implementing methods, algorithms, solutions for each of the three macro-stages of crisis management they are able to cover, namely Pre-Crisis management, Crisis management and Post-Crisis management. Each layer is designed to contain a set of architectural modules, including data sources, databases, and devices, that are logically and functionally related to the others belonging to the same layer. Moreover, they are interconnected through software connectors. Specifically, each layer acts, at the same time, as a server and as a client, respectively providing and consuming functionalities, and services.
The architectural modules belonging to the architecture layers that cover CIP management phases, before, during and after the crisis.
Achievement #5: Design of the Risk Assessment framework
Another important achievement of the first project year is the design of the Risk Assessment framework. In the 7SHIELD project, the Risk Assessment Framework is part of the components that are focused on the Prevention and Preparedness phases of an emergency. It combines the assessment of risk coming from natural hazards and cyber-physical threats with a method to analyse cascading effects of complex threats.
This methodology leverages the modellization of the pilot infrastructure, performed by the Model based Design and Assessment (MBDA) tool. The model contains the assets that are subject to threats and hazards and their interfaces. It constitutes the starting point for the evaluation of severity of impact and likelihood of cyber-physical threats and natural hazards, performed by the DiVa and CIRP tools, respectively.
The Digital Vulnerability Assessment (DiVa) component focuses on the identification and estimation of cyber vulnerabilities to enhance the risk analysis of cyber threats. Through DiVa, security officers can evaluate threats exposure, by leveraging on the identified set of characteristics (i.e. networking information, operational capabilities) of the infrastructure in order to evaluate its Cyber Maturity Model. The outcomes of the analysis will support the overall risk assessment process.
The Critical Infrastructure Resilience Platform (CIRP) is focused on the impact calculation and risk assessment of natural threats. CIRP analyses the structural capabilities of the infrastructures, and executes multiple what-if scenarios on the given infrastructure, in order to assess the impact of various natural threats on them. The results of this impact analysis will be combined with the likelihood of these threats in order to estimate the overall risk index of the infrastructure against natural threats.
The assessment of risks will be enriched with a technique of analysis of cascading effects performed by the MBDA tool and based on the definition of various dependencies among assets in the model of the pilot infrastructure. This technique allows the assessing of risks due to nth-order dependencies and the detection of high impacts that would otherwise not appear if only the immediate risk caused by a threat is considered.
The analysis carried out in the framework during the pre-crisis phase are visualized to the operators that can better plan response and mitigation actions.
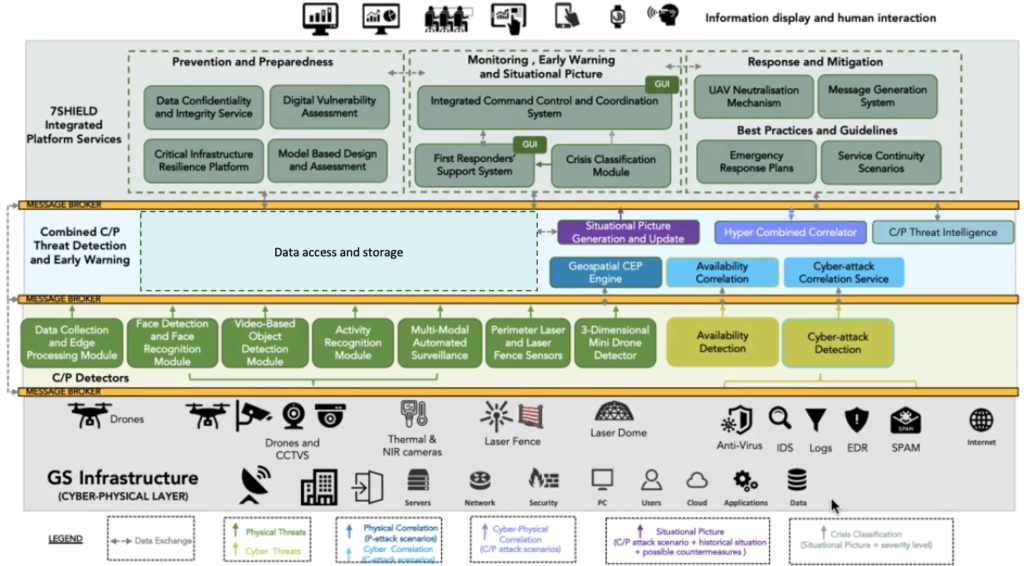
Achievement #6: Definition and Development of the 7SHIELD Detection & Correlation technologies
During the first project year, important achievements have been realised in terms of the innovative technologies to detect human-made and/or cyber-attacks and the efficient correlation of them. The discovered valuable information is provided to the operators and crisis managers to respond and confront an attack. Therefore, in the 7SHIELD ecosystem are deployed physical detection tools that are able to detect and notify useful information and events captured by CCTVs, UAVs, thermal cameras and laser sensor, along with cyber-security related probes which are able to identify cyber-attacks. The aggregation and fusion modules (correlators) process the data coming from the 7SHIELD detectors to extract and generate relevant information and malicious or abnormal events from them. A brief description of the deployed technologies in the 7SHIELD framework follows starting from the physical and cyber-attacks detectors and followed by the correlators.
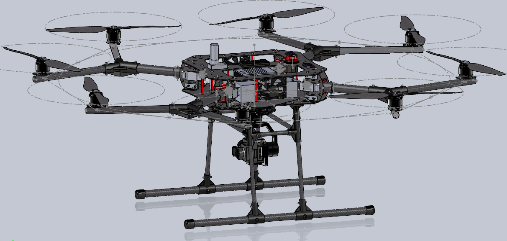
- Data collection and edge processing module: The 1st prototype of the 7SHIELD UAV has been developed and released. It is fully customised enables to accommodate the various hardware components (e.g. height/distance sensors, cameras) in order to perform on-board image processing making use of deep learning-based techniques. Modern commercial on-board sensors capable for surveillance operation mainly is utilised, such as: Visible light sensors (RGB), Multispectral sensors. The role of sensors, embedded in 7SHIELD UAV, is to acquire high-spatial and temporal images that can facilitate the surveillance of a specific area (covering a predetermined distance/radius around the ground stations). 7SHIELD UAV will be able to operate under different modes:
- Scheduled mode: during this mode, it will execute scheduled missions on specific areas. In this mode 7SHIELD UAV will be able to follow a predefined path autonomously;
- Alert mode: during this mode, it will fly manually (when a possible illicit activity will be reported) to the incident area and it will inspect (the embedded camera will autonomously inspect the whole area) for suspicious objects and moves.
Additionally, 7SHIELD UAV will support the surveillance missions of 7SHIELD ecosystem, during extreme weather conditions and/or inaccessible areas around space infrastructures.
- Face Detection and Recognition (FDR) module: The objective of the FDR module is to process video streams, in order to detect and recognize faces that may belong to suspicious individuals. Enabled through state-of-the-art deep learning facial recognition models, the FDR module can monitor critical infrastructure areas, where the human faces captured by CCTV cameras will be first detected by the Face Detection component and then further processed by the Face Recognition component in order to verify authorized matches with an authorised personnel database. Upon successful integration of the module to the 7SHIELD platform, its main outcome will be the production of alerts whenever a person cannot be successfully verified as an authorised individual. So far, the analysis of offline video files has been developed and evaluated, while in the following months the tool will be upgraded to enable real-time analysis of video streams coming from CCTV cameras.

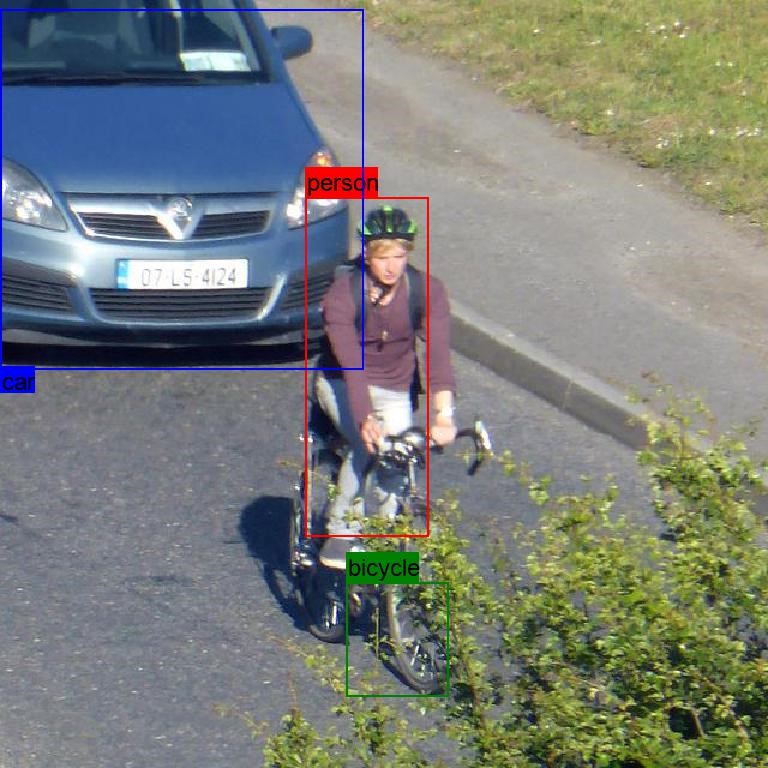
Video-based Object Detection (VOD) and Activity Recognition (AR) modules: The VOD module aims to process video streams or still images in order to locate and recognize objects of interest in the provided sources. Additionally, after detecting any human presence in the scene the corresponding results of object detection will be propagated to the AR module to identify suspicious and harmful activities. The main purpose of these modules is the accurate and efficient visual interpretation of the surroundings of the surveillance area. Specifically, the VOD module will utilise deep learning techniques in order to visually locate and identify the object of interest in the Critical Infrastructure area. The input of the module will be video streams which will be processed by a series of neural network layers expanding in large depth in the network. Each processed frame will provide information about the detections in it but there will be also connection with the following frames to increase the awareness of the system. Therefore, the output of this module will be:
-
- Awareness of surroundings via detected objects and individuals
- Bounding boxes and class label for each instance of interest
A “lighter” version of the aforementioned approaches can be embedded in GPU aiming to process video content at the edge. This lighter version will run on the autonomous 7SHIELD UAV and will be capable to perform on-board image/video processing by focusing on object detection from captured videos by the drone. By following this approach, the system’s surroundings awareness will be increased and will cover areas not covered by the fixed position cameras of the surveillance system.

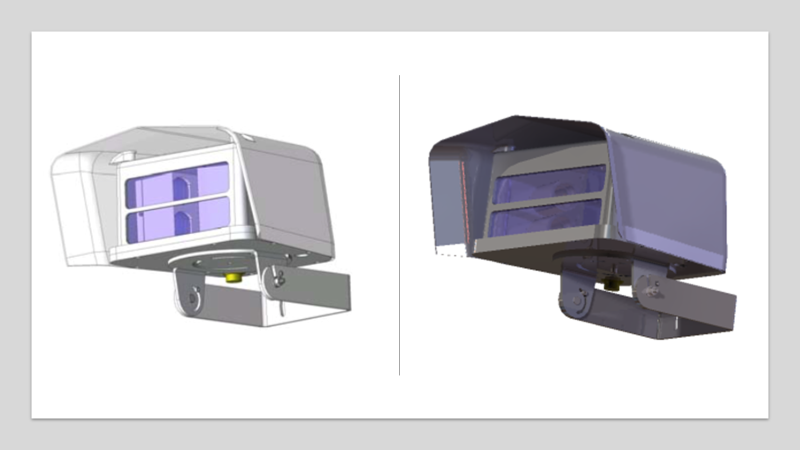
- Thermal and near-infrared image processing for man-made threats detection: The main output of this task is the development of a MultiModal Automated Surveillance (MMAS) system. The purpose of the MMAS is to detect possible threats through the use of video images that are within a Field of View (FoV) of a thermal camera. The developed algorithms produce alarms based on:
- heat level,
- movement and
- classification (reindeers, vehicles and persons)
Specifically, the MMAS system is based on a network of Near-InfraRed (NIR) and Thermal EO sensors that are supported by multiple processing servers, which process the video images from cameras and send the alarms to the core of the 7SHIELD platform. Multiple correlators will determine if the alarms are real threats. The MMAS is composed also by a User Interface (UI) that permits an operator to monitor the area under surveillance, configure and set the alarms. The FoV, the area of interest and the time that the camera is positioned on a FoV are also programed in the UI. The system is expected to assist but not totally substitute the operator. The goal is to make the work of camera operators more efficient and effective minimizing the tiredness of operators. Alerts should be generated whenever the system detects that an object has a suspicious behavior, detected using a rule-based system.
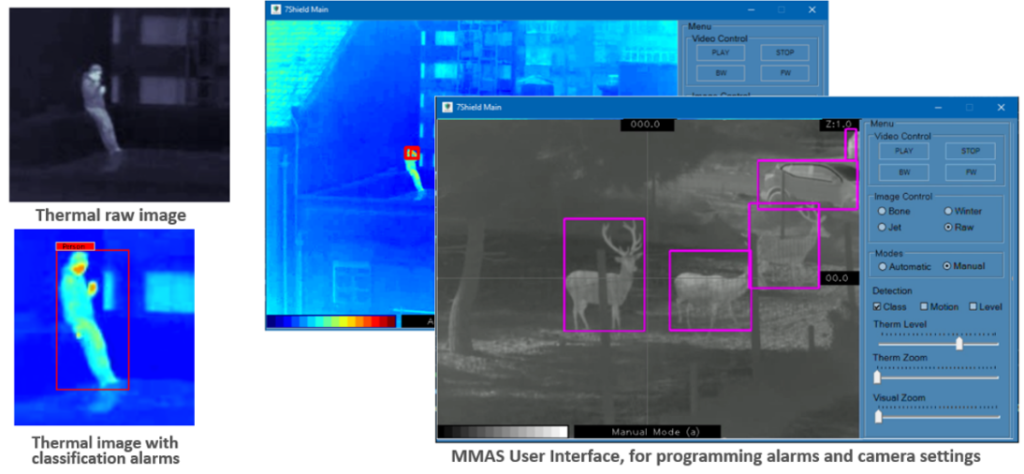
The MMAS processing unit performs image processing based on NIR and Thermal images/video making use of Machine Learning-based techniques, namely Convolutional Neural Networks (CNN) to classify three kinds of entities; reindeers, vehicles and persons. The movement alarms are based on the differences of images, from two or more video frames. The images frame rate and processing rates are chosen based on the velocity of the objects to be detected. The filtering techniques are also applied in order to not detect repetitive movements, like the movements of leaves in a tree. Finally, the simplest detection method is the level detection of heat. The alarms are based on the level of heat that is detected by the thermal cameras. This feature is very important because it permits to detect human, animal and vehicles whenever the above algorithms fail. The MMAS is ready to be integrated with the 7SHIELD and perform the first integration tests.
- Detection of ground based and aerial intruders
Perimeter Laser Sensor (PLS) and Laser Fence Sensor (LFS) are two DFSL’s innovative 2-dimensional laser-based detection systems with slaved PTZ cameras, to be incorporated with dedicated software and DFSL proprietary algorithm – for detection of human and vehicular intrusion on the ground level, and connectivity to state-of-the-art nodes and modern technologies.
The 3-Dimensional Mini drone (3D-MND) detector is the DFSL’s innovative 3D laser-based detection system with slaved camera, to be incorporated with specially developed DFSL software – for detection of drones over the sky of the pilots against aerial threats from drones.


Perimeter Laser Sensor (PLS) and Laser Fence Sensor (LFS)
Currently, the first prototypes of PLS, LFS and 3D-MND have been deployed, fulfilling the 7SHIELD requirements. For integration purposes with the 7SHIELD platform, a customised Universal Local Server (ULS) has been also developed and its communication with the platform is tested and evaluated. Simultaneously, False Alarm Rate (FAR) trials are in progress so as to improve the performance of the three components, aiming to be ready during the upcoming pilot use cases.
- Cyber-Attack Detection (CAD) framework: The Cyber-Attack Detection Framework aims to improve – at different levels – the security of critical infrastructures, specifically for the space industry. The framework is meant to provide an architecture of non-invasive security tools, which can be easily integrated in existing systems of the organization. The tools can also be adopted in subsets to protect confidential data from attacks occurring on different areas of these systems.
The Cyber-Attack Detection framework is capable of collecting security events from end-node sensors, correlating events coming from heterogeneous sources, providing analytics on the status of the system and raising alerts in case of dangerous scenarios. The framework consists of three main components:
- The Cyber-Attack Detection Layer
- The Cyber-Attack Correlation Layer
- The Graphical User Interface
The systems are initially monitored through the Cyber-Attack Detection Layer. It consists of a set of cyber security related probes and it is installed on sensitive end-nodes, providing a first level of threat detection. The probes cover several fundamental tasks such as system vulnerability scanning and preliminary malware detection, network traffic inspection, file integrity monitoring, components availability monitoring and so on.
All the events produced by the Cyber-Attack Detection Layer are sent to the Cyber-Attack Correlation layer. This layer is a trusted execution-based privacy aware Security Information and Event Management (SIEM) capable of performing complex data processing. In this layer the events are collected, stored, classified, processed and correlated together through ad-hoc correlation rules, in order to detect complex attack patterns. This module uses secure communication protocols and a hardware supported Trusted Execution Environment (TEE) in order to guarantee the confidentiality and integrity of the data transiting, resting and also being processing.
All the events collected and processed are displayed in the Graphical User Interface (GUI), allowing an easier recognition of the incoming cyber-attacks. The GUI consists of a set of different security dashboards, displaying:
- All the alerts generated by the correlation layer
- The visualization of suspicious events related to the security probes and the system / application logs
- Analytics through bar charts, histograms, maps, pie charts etc.
- A bird eye view of the overall security system status
The Cyber-Attack Detection Framework has been created to combine the systems already used by the organizations with a system intended for monitoring the security of the ground segment systems, applications and services. The framework creates an “overlay” architecture of add-on components that enhances data security in a transparent fashion. The Cyber-Attack Detection Framework has been successfully deployed and tested in the first pilot use cases demonstration.
- Combined C/P threat detection and early warning module and geospatial event correlator: The alerts generated by the cyber and/or physical detection tools proceed for further analysis and correlation in order to identify timely and efficiently potential complex cyber, physical and hybrid attacks. Hence, in the 7SHIELD framework, the Geospatial Complex Event Correlator (G-CEP) correlates disparate events/information detected by the physical sensors on the field (e.g. cameras, drones, laser sensors etc.). The correlation of these events/information will be based on the characteristics and content of these events, e.g. timewise, geospatial characteristics etc. Currently, the first prototypes of the G-CEP component have been deployed, fulfilling the 7SHIELD requirements. A number of correlation rules and patterns has been defined and implemented, in order to support the correlation of the events that are detected by the physical sensors. This list of events will be further refined and updated during the next period according to the requirements and the scenarios of the upcoming pilots. The result of the G-CEP component is forwarded to the Hyper Combined Correlator (HCC) and the Situational Picture Generation & Update (SPGU) modules for further analysis and assessment of the situation on the field. All messages that are received and processed by the G-CEP component are based on the IDMEFv2 (Intrusion Detection Message Exchange Format) message format.
The Availability Detection Monitoring (ADM) aims to monitor availability of configured components and generate alerts in case of a critical status change. CS Novidy’s contributes to the 7SHIELD project where it provides availability monitoring and hyper correlation services for the 7SHIELD partners. The availability monitoring module is based on CS Novidy’s expertise in availability monitoring. It has been deployed on two “Pilots Use Case” (PUC) and used successfully so far.
The hyper correlator, called Hyper Combined Correlator (HCC), is based on the Unity 360 solution developed by CS GROUP and makes use of the new IDMEFv2 format designed by the SECEF project to handle data from different kinds of sources (availability monitoring, security monitoring, and so on). This new type of correlator is used by the 7SHIELD project to provide hybrid correlation, correlating data from both the cyber and physical worlds, to detect new emerging threats.
Engineering, with several years of experience in development of Situational Awareness applications in the context of Critical Infrastructure Protection (CIP) projects, provides an important contribute to the 7SHIELD system with the Situational Picture Generation & Update (SPGU) module.
The main aim of the SPGU is to build and maintain a clear Situational Picture of the SGS that the 7SHIELD system is monitoring. The main sources of information exploited by the SPGU are represented by the 7SHIELD correlation modules (cyber, physical and hybrid) and by any 7SHIELD tool able to provide useful information can contribute to the creation of the Situational Picture.
Every complex event generated by the 7SHIELD correlations is processed by the SPGU module to further enrich the Situational Picture of the SGS. Moreover, the SPGU correlates the information with those coming from the tools included in the prevention and preparedness phase or in the response and mitigation phase. Among the others, the Situational Picture includes the following information:
- what is currently happening including information about each event that is involved into the current situation;
- an estimation of the criticality, by considering the information provided by the prevention and preparedness tools the actions were activated, or can be activated, as response of the identified events and to mitigate the related consequences;
- the status of the SGS infrastructure.
The Situation Picture will be exploited by the 7SHIELD system to provide to the SGS user a clear view of the current status of its assets.
Achievement #7: Design and development of the Cyber and Physical Threat Intelligence (CPTI) component
Social Media platforms has changed the way of communication between people. These platforms allow users and organizations to communicate each other, sharing their ideas, interests, and knowledge, becoming a part of their daily routine. An estimated 2.94 billion people globally use social media. On the other hand, social media platforms represent good channels to exploit for perpetrating various kind of crimes and illegal activities in several areas, including cyber-crimes and terrorism. For this reason, shared content in social media / blogs / forums posts needs to be tracked to determine what they contain through post information extraction
Cyber and Physical Threat Intelligence (CPTI) component, developed by ENG for the 7SHIELD project, can identify suspicious activity on surface web and social media and extract relevant contents and clues from dark nets. In fact, continual monitoring of social media platforms has been pointed out by security practitioners and policy makers as part of a comprehensive cybersecurity intelligence
strategy to protect EU citizens and their business activities. CPTI components uses artificial intelligence and deep learning algorithms to extract text data (such as tweets or posts on blogs, forums, and social networks); to analyze language, and to identify possible threats using a pre-trained algorithm on specific threats.
This component is a key feature for the pre-crisis phase of the project. In fact, identify possible threats in social media / blogs / forums posts represents an early warning mechanism that can reduce the risk of an occurence of a cyber or physical attack.
Achievement #8: Design and development of the 7SHIELD secure authentication mechanism
Single sign-on (SSO) and other robust secure authentication and authorization mechanisms are necessary for mitigating and preventing cyber-attacks to critical satellite data storage systems. SSO-like solutions have been shown to improve security, usability and infrastructure maintenance while improving the end user’s convenience and trust. Nowadays the usage of passwords is being gradually abandoned for several reasons. Passwords are often the weak link and the main target for malicious actors. Passwords are the root cause of over 80% of data breaches since up to 51% of passwords are reused. Malicious actors can use passwords and other credentials from data leaks of compromised services to further exploit user accounts from non-compromised services.
7SHIELD is proposing an innovative Secure authentication mechanism ensuring secure personal data storage, secure encrypted personal data search, expressive and advanced access control over encrypted data and secure data integrity verification. The Secure authentication mechanism will use the hybrid encryption mode that elegantly merges symmetric encryption, attribute-based encryption, proxy re-encryption and searchable encryption.
Moreover, blockchain and Multi-Factor Authentication technologies will be used to ensure Confidentiality, Integrity, Availability of transmitting protected information from falsification or modification and providing the user with an additional authentication method (through the usage of hardware components in the form of secure elements, such as smart cards and SIM cards, as well as social logins).
The Secure authentication mechanism proposed is designed based on outputs of previous and existing projects, technologies, and architectures. It uses a cloud-based Identity, Access Management mechanisms and different authentication/authorization technologies such as OpenID Connect. In terms of operability, a container-based microservices architecture – Kubernetes clusters orchestration – guarantees the high availability of the authentication and authorization service and the integration with other 7SHIELD modules provides an additional robustness layer in case of unavailability.
This Secure authentication mechanism will be used by all the 7SHIELD modules which require user authentication, and its scalable deployment guarantees further applications in multiple contexts.
Achievement #9: First operational test of 7SHIELD on the ONDA DIAS (Copernicus’ Data & Information Access Services)
OVERVIEW
ONDA is one of the DIAS (Data and Information Access Services), a platform providing access to satellite data and Cloud resources for users to develop and host their own applications.
The ONDA DIAS Cloud infrastructure has been updated in order to use the modules for preventing, detecting and reacting to any cyber-attack developed in the 7SHIELD project. The 7SHIELD framework demonstrated to improve the protection of the services offered to ONDA end users: namely the Discovery (Catalogue Graphical User Interface), View (allowing visualization of data on the world map through a standard Web Map Service) and Download (for which user registration to ONDA is required).
SIMULATED ATTACKS
Three types of cyber-attacks were simulated:
-
- Man in the middle attack
- Denial of Service attack
- Ransomware attack
PILOT EXECUTION DATES AND PARTNERS INVOLVEMENT
The Pilot demonstration took place in the period from 19 September to 22 October. 9 partners have been actively involved in the test’s execution and more than 50 people attended to the real exercise for demonstration organized by SERCO on 13, 15 and 22 October.
EVALUATION
As a result of the PUC, 9 Key Results of the 7SHIELD project have been tested. In particular:
7SHIELD ensures the assessment of the risks and weakness of a service operating in the Earth Observation context and provides the users with an instrument to predict cyber-attacks by identifying suspicious activities on social media. The usage of the innovative Single Sign-On system ensures the secure authentication, integrity, and confidentiality of user data.
The technologies provided by 7SHIELD are potentially detecting any type of cyber-attack and demonstrated to offer a complementary protection to the currently adopted detection methodology already in operation on ONDA. The emergency response plan and its visualization in the graphical user interface proved to be an advantage, improving the actual efficiency in response in case of a cyber-attack.
Achievement #10: Second operational test of 7SHIELD on the ICE Cubes Service (ISS International Commercial Experiment Cubes)
OVERVIEW
The International Commercial Experiment Cubes service (ICE Cubes) is a commercial service that offers access to space for research, technology, and education. It allows public or private entities to run their experiments on board the International Space Station for access to microgravity.
7SHIELD is being deployed within the ICE Cubes infrastructure, providing a comprehensive framework covering the phases of cyber-attack: Prevention and analysis of potential weaknesses on the ICE Cubes infrastructure, detection of attack on the service, support for the ICE Cubes operators and security staff to mitigate the attacks.
The ICE Cubes infrastructure was duplicated to create a reference environment allowing to execute a number of cyber-attacks, without disrupting flight operations, and allowing ICE Cubes operators to evaluate the 7SHIELD first prototype.
SIMULATED ATTACKS
The attacks were performed by malicious users of the ICE Cubes service. Three types of cyber-attacks were executed:
-
- Login brute force attack, attacking the 7SHIELD authentication module
- Denial of Service attack, attacking telemetry distribution systems of the ICE Cubes system
- User escalation privileges attack, performed at the edge of the system, in one of the Experiment Cube.
PILOT EXECUTION DATES AND PARTNERS INVOLVEMENT
The ICE Cubes Pilot demonstration took place in the period from 15th November to 29th November. 9 partners (SERCO, ENG, NOA, SATWAYS, CERICT, KEMEA, RESIL, SPACEAPPS, CSNOV) have been actively involved in the test’s execution and more than 50 peoples attended to the real exercise for demonstration organized by SpaceApps on the 17 and 29 November.
EVALUATION
As a result of the PUC4, the 7SHIELD framework has been tested in a new ground segment operational environment, with operational constraints very different from the previous evaluation on PUC5 ONDA.
Nine Key Results of the 7SHIELD project have been tested and evaluated. All phases of a cyber-attack could be managed via 7SHIELD and evaluated within the ICE Cubes environment.
The ICE Cubes service benefited from the comprehensive security framework implemented by 7SHIELD:
-
- User interfaces centralizing the security status of the service: service status and reports, threat and environment forecast, attack detections, crisis responses;
- Improved cyber-attack detections: awareness status, correlation of threat detection sources;
- Tracking and reporting of attacks, responses, updates, notifications to the operators and security officer.
Publications
7SHIELD partners are actively involved in European research activities and workshops and are advancing knowledge in several cutting-edge areas. You will find below their latest conference papers, publications and scientific papers.
|
Date |
Title |
Author(s) |
Journal / Link |
|
30/04/2021 |
A social media analytics platform visualising the spread of COVID-19 |
S. Andreadis, G. Antzoulatos, T. Mavropoulos, P. Giannakeris, G.Tzionis, N. Pantelidis, K. Ioannidis, A. Karakostas, I. Gialampoukidis, S. Vrochidis, I. Kompatsiaris |
https://www.sciencedirect.com/science/article/pii/S2468696421000185 |
|
08/10/2021 |
Severity level assessment from semantically fused video content analysis for physical threat detection in ground segments of space systems |
G. Antzoulatos, G.Orfanidis, P.Giannakeris, G. Tzanetis, G.Kampilis-Stathopoulos, N.Kopalidis, I.Gialampoukidis, S.Vrochidis, I. Kompatsiaris |
2nd International Workshop on Cyber-Physical Security for Critical Infrastructures Protection (CPS4CIP 2021). https://doi.org/10.5281/zenodo.5567020
|
|
22/11/2021 |
A MDE Tool for Security Risk Assessment of Enterprises |
E. Schiavone, N. Nostro, F. Brancati |
Industrial Track of LADC 2021, the 10th Latin-American symposium on Dependable Computing, November 22-26 2021. |
Upcoming events
7SHIELD partners will attend the following events. We would be delighted to meet you there!
-
- Industry Space Days 2021, 7-8 December (virtual event)
- CIPRE-EXPO (2021 Critical Infrastructure Protection and Resilience Europe), 15-17 March 2022 (Bucharest, Romania)
- 7SHIELD International Workshop on Security Standardisation Strategy and Policy-planning, Q1 2022
An international workshop on Security Standardisation Strategy and policy-planning, organised by the 7SHIELD consortium, will be held in Q1 2022.
-
- 7SHIELD Info Day, Q4 2022
A 7SHIELD Info Day will be held in Q4 2022, location to be determined. It will be the opportunity to share the project’s experiences and lessons learnt and will contribute to the dissemination of the 7SHIELD results.
If you are interested in participating to the next 7SHIELD events, please contact us!
Latest news
Due to the COVID-19 pandemic, the project duration should be extended until February 2023. This time extension should enable the partners to organize physical meetings to perform the different operational test campaigns and demonstrations on FMI’s, SERCO’s, NOA’s, DEIMOS’s and SPACEAPPS’s infrastructures.